A sender sends encrypted message to an intended receiver. If the sender also wishes to send evidence of
his identity to the receiver, he encrypts a piece of information that makes
sense to both, using his private key and sends it to the receiver. This encrypted piece of information is called
the digital signature. Receiver uses
sender's public key to decrypt sender's digital signature and to retrieve the
information. If this information
decrypts sensibly, receiver can be sure of the identity of the sender because
digital signature must have been created using the private key that pairs with
sender's public key.
This can also be used to ensure that sender does not repudiate at later
stage. The piece of information that
makes sense to both is in fact related to the actual message that is the
subject of transmission.
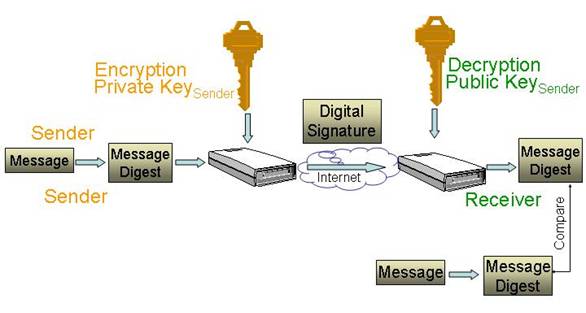
The piece of information is called the message digest
and is generated from the actual message using some algorithm that the parties
agree upon. One-way hash
function is generally used as the algorithm for the creation of message
digest.
- Sender
generates message digest from the message, using one-way hash function as
the algorithm.
- Sender
encrypts message digest, using his private key and product is called digital
signature.
- Sender
sends digital signature to the receiver over the Internet.
- Receiver
then does two things:
- Receiver
recovers message digest by decrypting the digital signature using
sender's public key.
- Receiver
generates message digest by applying one-way hash function to the message
that has also arrived.
- Receiver
compares the two versions of message digest.
If the two versions of message digest compare, sender must have signed it
and receiver can be sure of sender's identity.
This also means that the sender can not later deny having sent the
message (sender can not repudiate) because he must have signed the message
digest.
|
Go
to http://www.amazon.com. Check their digital certificate and find
out what algorithm is used to generate digital signature. |
|
|
|
Creation
of digital certificate is in essence public key cryptography in reverse. Explain. |
|
|